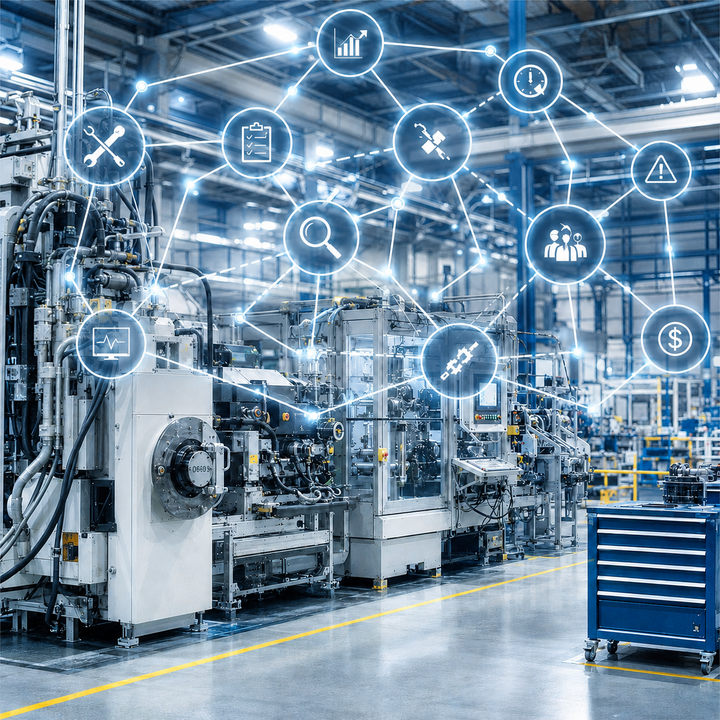
At a manufacturing company, a key production line has been running reliably for years. It is precisely this stability that breeds complacency. Maintenance schedules are pushed back to handle order spikes. Spare parts are ordered later. While inspections are carried out as a matter of formality, their technical depth diminishes. In the risk report, the issue is listed as a general "operational risk"—without a clear distinction between cause, event, effect, and corrective actions.
Then a critical unit fails. The production line comes to a standstill. At first, the damage seems limited: a technical problem, a repair, some overtime. Only gradually does it become apparent that the real damage is occurring beyond the factory floor. Delivery dates are missed. Expedited shipping drives up delivery costs. Customers postpone orders. Restoration costs rise, and sales must revise the revenue forecast. A lack of maintenance turns into a business interruption; the business interruption becomes a company-wide management problem.
This is precisely where many traditional risk inventories reach their limits. They identify the risk but fail to clearly explain the underlying logic: What causes drive the event? What measures or barriers should prevent the transition? What consequences arise if recovery measures fail or are only partially effective? The Bow-Tie analysis is well-suited for this kind of structuring. A Bayesian network is suitable for probabilistic evaluation.
The Anatomy of a Bow-Tie Analysis
The bow-tie analysis is a scenario-based structuring method. At its core is the top event: the moment when control over a critical process is lost. To the left of this are causes or threats; to the right are consequences. Between causes and the Top Event lie preventive barriers; between the Top Event and consequences lie mitigating or recovery-oriented barriers. The graphical form resembles a bow tie—hence the name "Bow-Tie."
Methodologically, it is important to clearly separate three levels: cause, event, and effect. This separation is by no means trivial. In practice, the same terms are often used across multiple levels. "Business interruption," for example, is sometimes referred to as a cause, then as an event, and later as a consequence. The Bow-Tie, on the other hand, enforces conceptual discipline. This improves not only clarity but also subsequent quantification.
![Fig. 01: Anatomy of a bow-tie analysis using the example of a production outage [Source: Author’s own illustration] Fig. 01: Anatomy of a bow-tie analysis using the example of a production outage [Source: Author’s own illustration]](/fileadmin/_processed_/c/2/csm_Fig-01_BayesNet_20260506_8b7216fcb3.png) Fig. 01: Anatomy of a bow-tie analysis using the example of a production outage [Source: Author’s own illustration]
Fig. 01: Anatomy of a bow-tie analysis using the example of a production outage [Source: Author’s own illustration]
The strength of the bow-tie lies in its clarity and its suitability for workshops. Business units, maintenance, controlling, risk management, and internal audit can all discuss the issue using a common model. The method is particularly well-suited for identifying preventive and reactive barriers. It not only shows that a risk exists, but also at which stage it should be prevented or its impact mitigated.
Its limitations arise where probabilities, dependencies, and updates to the evidence become relevant. While a bow-tie can indicate that the failure of multiple barriers is critical, it does not automatically calculate how much this changes the probability of the top event occurring. It also leaves open how new information—such as overdue maintenance orders or an untested emergency plan—changes the picture. This is precisely where Bayesian networks come into play.
The Anatomy of a Bayesian Network
Bayesian networks—also known as Bayes networks or Bayesian belief networks—are probabilistic graphical models. Formally, they consist of nodes and directed edges. The structure is a directed acyclic graph (DAG). "Directed" means that the edges have a direction of influence. "Acyclic" means that there are no closed loops within the graph structure.
Each node represents a variable, such as "poor maintenance," "equipment failure," or "decline in sales." Each node has states, such as yes/no or low/medium/high. The edges model directed dependencies. A conditional probability distribution is defined for each node. For parent nodes, this is a prior distribution; for dependent nodes, it consists of Conditional Probability Tables (CPTs).
![Fig. 02: Anatomy of a Bayesian network [Source: own illustration] Fig. 02: Anatomy of a Bayesian network [Source: own illustration]](/fileadmin/_processed_/3/3/csm_Fig-02_BayesNet_20260506_920626771f.png) Fig. 02: Anatomy of a Bayesian network [Source: own illustration]
Fig. 02: Anatomy of a Bayesian network [Source: own illustration]
The methodological core of a Bayesian network is the decomposition of a complex overall probability into local conditional probabilities. In practical terms, this means that the probability of a system failure is not treated as an isolated point value, but rather as a function of its parent nodes, such as inadequate maintenance, lack of inspection, and insufficient barriers. The model is thus specified locally and interpretable globally.
In simplified terms, the logic can be expressed as: P(equipment failure | maintenance, inspection, barrier). If new evidence is added—such as the finding that several maintenance tasks are overdue—the model updates the posterior probabilities of the dependent nodes. This update is the key added value compared to static risk profiles.
Typical types of inference include:
- Forward inference: Known causes are used to infer the top event and its consequences.
- Backward diagnosis: Observed damage or failures are used to infer probable causes or barrier failures.
- What-if analysis: The impact of improved or degraded barriers on the chain of effects is examined.
- Sensitivity analysis: An investigation is conducted to determine which nodes or barriers have the greatest impact on the overall risk.
A good Bayesian network does not start with many nodes, but with a clean structure. Modeling decisions primarily concern granularity. Should "maintenance" be modeled as a single node or broken down into sub-nodes such as inspection, spare parts management, and condition monitoring? Are conditions recorded as binary or multi-level? How are organizational factors such as budget constraints or staff shortages modeled? These decisions determine whether the model will be actionable or merely appear precise.
The methodological link: The bow-tie becomes a Bayesian network
The relationship is methodologically clear: the bow-tie provides the substantive logic, while the Bayesian network provides the probabilistic formalization. A bow-tie can be translated into a directed acyclic graph model by modeling its elements as nodes and its cause-and-effect relationships as directed edges. This translation is not merely a graphical representation but an analytical condensation.
Threats typically become parent nodes. Preventive barriers are modeled as state nodes whose values influence the probability of the top event. The top event becomes the central event node. Mitigating barriers influence the probabilities or the severity of the consequences. Consequences become child nodes. Escalation factors can be introduced as additional influence nodes that make barrier failure more likely or exacerbate the damage.
| Bow-Tie Element | Translation into a Bayesian network |
|---|---|
| Cause / Threat | Parent node that influences the probability of the top event |
| Preventive Barrier | Influence node with states such as active / partially active / inactive |
| Top Event | Central event node, often modeled as binary or with few failure levels |
| Reactive Barrier | Impact node on the damage side that modifies recovery or consequential damage |
| Consequence | Child node with damage states, such as low/high recovery costs |
| Escalation Factor | Additional node that weakens barriers or amplifies effects |
Table 1: Methodological translation of bow-tie elements into a Bayesian network
![Fig. 03: From the bow-tie structure to the Bayesian network [Source: author’s own illustration] Fig. 03: From the bow-tie structure to the Bayesian network [Source: author’s own illustration]](/fileadmin/_processed_/4/f/csm_Fig-03_BayesNet_20260506_4ed81380b4.png) Fig. 03: From the bow-tie structure to the Bayesian network [Source: author’s own illustration]
Fig. 03: From the bow-tie structure to the Bayesian network [Source: author’s own illustration]
A practical guide in five steps
The combination of bow-tie analysis and Bayesian networks should not be viewed as a purely technical modeling exercise. A step-by-step approach is crucial: First, the risk scenario is clearly structured from a technical perspective; then, this structure is translated into a probabilistic model. This ensures that the analysis remains understandable to subject matter experts while also providing a quantitative level of evaluation. The following five steps show how a workshop-ready Bow-Tie analysis is transformed into a computable Bayesian network.
![Fig. 04: A practical guide in five steps [Source: own illustration] Fig. 04: A practical guide in five steps [Source: own illustration]](/fileadmin/_processed_/1/4/csm_Fig-04_BayesNet_20260506_2f41ececdb.png) Fig. 04: A practical guide in five steps [Source: own illustration]
Fig. 04: A practical guide in five steps [Source: own illustration]
Step 1: Create a Bow-Tie Analysis in the Workshop: The first step is a robust bow-tie analysis. For this practical example, the top event is not a generic "production risk," but rather the specific "failure of the central production line X200." On the left, the causes are identified: insufficient maintenance, overdue inspections, missing spare parts, outdated components. On the right, the impact scenarios are differentiated: high recovery costs, delivery delays, decline in revenue, loss of customers. The methodological quality is already evident in this step: vague formulations are eliminated, barriers (measures) are specifically named, and escalation factors are identified.
Step 2: Derive Nodes: The nodes for the Bayesian network are derived from the bow-tie diagram. A deliberately simplified initial model can consist of seven nodes: inadequate maintenance, missing inspection, preventive barrier failure, top event "system failure," mitigating barrier failure, high recovery costs, and decline in revenue. More complex models can later incorporate organizational factors or financial secondary effects.
Step 3: Define states: Each node requires defined states. For a basic model, binary states are sufficient. In a more mature model, states can be graded, such as "effective / limited / ineffective." Observability is crucial. "Poor maintenance" should not merely be a hunch but should be verifiable through overdue work orders, missing inspection reports, or an increasing number of recurring malfunctions.
Step 4: Calibrate CPTs: The Conditional Probability Tables are the heart of the Bayesian network. They determine how strongly parent nodes influence a target node. In the practical example, therefore, the model determines how much poor maintenance, missing inspections, and barrier failures increase the probability of a system failure. These probabilities can be determined in various ways: through historical maintenance data, past damage incidents, expert assessments, technical reliability metrics, or a combination of these information sources.
| Inadequate maintenance | Inspection missing | Preventive barrier failed | P (Equipment failure) |
| no | no | no | 2 % |
| yes | no | no | 22 % |
| yes | yes | no | 40 % |
| yes | yes | yes | 72 % |
Table 2: Simplified illustrative CPT for the "Equipment Failure" node. The values are, of course, fictitious and are provided solely to demonstrate the method.
Step 5: Evidence and What-If Analyses: Once the model is in place, it can be operationalized. New evidence—such as a failure in condition monitoring or overdue maintenance packages—is fed into the model. This causes the posterior probabilities for the top event and its consequences to change. Measures can also be compared: Does an improved maintenance plan reduce risk more effectively than additional spare parts inventory? Does a tested recovery plan have a greater impact on revenue decline than generic crisis communication?
![Fig. 05: Example of a "what-if" analysis of a simple Bayesian network [Source: own calculations and illustration] Fig. 05: Example of a "what-if" analysis of a simple Bayesian network [Source: own calculations and illustration]](/fileadmin/_processed_/a/f/csm_Fig-05_BayesNet_20260506_26b5059b5f.png) Fig. 05: Example of a "what-if" analysis of a simple Bayesian network [Source: own calculations and illustration]
Fig. 05: Example of a "what-if" analysis of a simple Bayesian network [Source: own calculations and illustration]
Practical examples of the use of Bayesian networks for supplier risk assessment can be found in Chapter 10 of the current book *Data Analytics in Risk Management: Descriptive Analytics, Diagnostic Analytics, Predictive Analytics*
Romeike, Frank / Wieczorek, Gabriele (2026): Data Analytics in Risk Management – Descriptive Analytics – Diagnostic Analytics – Predictive Analytics, Springer Verlag, Wiesbaden 2026. [Currently available in German; an English version is planned]
More information
Data Quality and Model Risk
The most important warning is this: A Bayesian network does not make a bad bow-tie model good. It merely makes its assumptions explicit and mathematically visible. If the underlying structure is fuzzy, a fuzzy bow-tie model will not result in a good model, but only in a mis-model that appears precise.
In the practical example, the problem often begins at the structural level. If "declining sales" were modeled as the cause of the equipment failure, the direction of causality would be incorrect. If "maintenance" is recorded only in general terms as a barrier, without distinguishing between maintenance schedule, condition monitoring, and spare part availability, it remains unclear which measure is actually effective. If measures are formally marked as completed in the maintenance system even though only a visual inspection took place, the model overestimates the effectiveness of the barrier.
Data Quality Check
1. Is the top event precisely defined?
2. Are cause, event, and effect clearly separated?
3. Are barriers (preventive and reactive measures) observable, auditable, and not merely nominal? 4. Are conditions and data sources documented?
5. Are CPTs justified, validated, and updated regularly?
Fake data is particularly problematic. A Bayesian network is sensitive to systematically biased inputs. If the emergency plan is coded as "effective" in the model even though it has never been tested in real life, the model will underestimate the probability of high recovery costs and, consequently, the expected decline in revenue. The result is a false sense of security. This is precisely why the integration of risk management with maintenance, quality management, and emergency management/BCM is so important.
Conclusion
Bow-tie analysis and Bayesian networks are not competing methods. They complement each other. The bow-tie approach provides transparency, structure in scenario description, and concrete preventive or reactive measures. The Bayesian network adds conditional probabilities, dependency logic, evidence updating, and what-if analyses. Taken together, a workshop scenario gives rise to a more robust decision-making model.
The methodological core of this combination lies in the systematic analysis of cause-and-effect relationships. In this way, risk modeling ties in with a classic epistemological principle formulated by Immanuel Kant in the "Critique of Pure Reason": All changes occur according to the law of the connection between cause and effect. This idea is particularly central to risk management: risks do not arise randomly in a vacuum, but along causal chains, dependencies, barriers, and mechanisms of action. The Bow-Tie makes this causal structure visible; the Bayes Net makes it probabilistically evaluable.
The benefit lies not in mathematical complexity for its own sake, but in better risk intelligence. The model forces us to disclose assumptions: Which cause has how much impact? Which measures are actually effective? Which consequence occurs only when cause- or effect-related measures fail? And how good is the data on which this assessment is based? It is precisely this transparency that makes the combination of the Bow-Tie and Bayes Net so valuable in practice.
Bibliography and Further Reading
- Romeike, Frank (2019): Die Bow-Tie-Analyse (Toolbox), in: GRC aktuell, Ausgabe Februar 2019, 01/2019, p. 39-44. [in German language]
- Badreddine, Ahmed / Ben Amor, Nahla (2013): A Bayesian approach to construct bow tie diagrams for risk evaluation, in: Process Safety and Environmental Protection, 91(3), p. 159-171.
- de Ruijter, Alex / Guldenmund, Frank (2016): The bowtie method: A review, in: Safety Science, Vol. 88, p. 211-218.
- Khakzad, Nima / Khan, Faisal / Amyotte, Paul (2013): Dynamic safety analysis of process systems by mapping bow-tie into Bayesian network, in: Process Safety and Environmental Protection, 91(1-2), p. 46-53.
- Koller, Daphne / Friedman, Nir (2009): Probabilistic Graphical Models. Principles and Techniques, MIT Press, Cambridge, Massachusetts/London 2009.
- Romeike, Frank / Wieczorek, Gabriele (2026): Data Analytics im Risikomanagement - Descriptive Analytics - Diagnostic Analytics - Predictive Analytics, Springer Verlag, Wiesbaden 2026. [in German language; an English version is planned]